Certificate authorities
A CA is used to sign other server and client certificates. Different CAs can be used for different domains or certificates. For example, if your organization is international you may have a CA for each country, or smaller organizations might have a different CA for each department. The benefits of multiple CAs include redundancy, in case there are problems with one of the well-known trusted authorities.
Once you have created a CA certificate, you can export it to your local computer.
Local CAs
The FortiAuthenticator device can act as a self-signed or local CA.
To view the certificate information, go to Certificate Management > Certificate Authorities > Local CAs.
The following information in shown:
| Create New | Create a new CA certificate. |
| Import | Import a CA certificate. See Importing CA certificates and signing requests. |
| Revoke | Revoke the selected CA certificate. |
| Delete | Delete the selected CA certificate. |
| Export | Save the selected CA certificate to your computer. |
| Search | Enter a search term in the search field, then press Enter to search the CA certificate list. The search will return certificates that match either the subject or issuer. |
| Filter | Select to filter the displayed CAs by status. The available selections are: All, Pending, Expired, Revoked, and Active. |
| Certificate ID | The CA certificate ID. |
| Subject | The CA certificate subject. |
| Issuer | The issuer of the CA certificate. |
| Status | The status of the CA certificate, either active, pending, or revoked. |
| CA Type | The CA type of the CA certificate. |
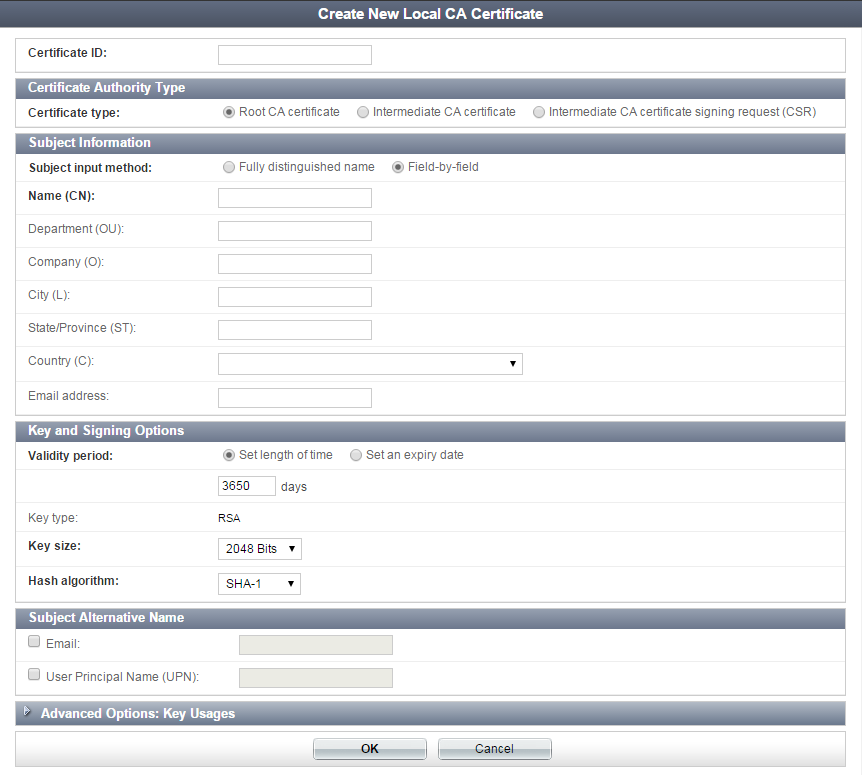
To create a CA certificate:
- From the local CA certificate list, select Create New. The Create New Local CA Certificate window opens.
- Enter the following information:
- Select OK to create the new CA certificate.
Importing CA certificates and signing requests
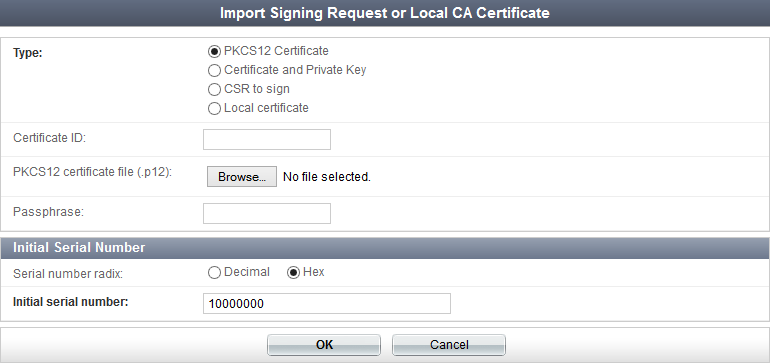
Four options are available when importing a certificate or signing request: PKCS12 Certificate, Certificate and Private Key, CSR to sign, and Local certificate.
To import a PKCS12 certificate:
- From the local CA certificate list, select Import. The Import Signing Request or Local CA Certificate window opens.
- Select PKCS12 Certificate in the type field.
- Enter the following:
- Select OK to import the certificate.
To import a certificate with a private key:
- From the local CA certificate list, select Import. The Import Signing Request or Local CA Certificate window opens.
- Select Certificate and Private Key in the type field.
- Enter the following:
- Select OK to import the certificate.
To import a CSR to sign:
- From the local CA certificate list, select Import. The Import Signing Request or Local CA Certificate window opens.
- Select CSR to sign in the type field.
- Enter the following:
- Select OK to import the CSR.
To import a local CA certificate:
- From the local CA certificate list, select Import. The Import Signing Request or Local CA Certificate window opens.
- Select Local certificate in the type field.
- Select Browse... in the Certificate file (.cer) field to locate the certificate file on your computer.
- Select OK to import the local CA certificate.
CRLs
A CRL is a file that contains a list of revoked certificates, their serial numbers, and their revocation dates. The file also contains the name of the issuer of the CRL, the effective date, and the next update date. By default, the shortest validity period of a CRL is one hour.
Some potential reasons for certificates to be revoked include:
- A CA server was hacked and its certificates are no longer trustworthy,
- A single certificate was compromised and is no longer trustworthy,
- A certificate has expired and is not supposed to be used past its lifetime.
Go to Certificate Management > Certificate Authorities > CRLs to view the CRL list.
The following information is shown:
To import a CRL:
- Download the most recent CRL from a CDP. One or more CDPs are usually listed in a certificate under the Details tab.
- From the CRL list, select Import.
- Select Browse... to locate the file on your computer, then select OK to import the list.
When successful, the CRL will be displayed in the CRL list on the FortiAuthenticator device. You can select it to see the details (see To view certificate details:).
Locally created CRLs
When you import a CRL, it is from another authority. If you are creating your own CA certificates, then you can also create your own CRL to accompany them.
As a CA, you sign user certificates. If for any reason you need to revoke one of those certificates, it will go on a local CRL. When this happens you need to export the CRL to all your certificate users so they are aware of the revoked certificate.
To create a local CRL:
- Create a local CA certificate. See Local CAs.
- Create one or more user certificates. See End entities.
- Go to Certificate Management > End Entities > Users, select one or more certificates, and then select Revoke. See To revoke a certificate:.
The selected certificates will be removed from the user certificate list and a CRL will be created with those certificates as entries in the list. If there is already a CRL for the CA that signed the user certificates, the certificates will be added to the current CRL.
|
|
If, at a later date, one or more CAs are deleted, their corresponding CRLs will also be deleted, along with any user certificates that they signed. |
Configuring online certificate status protocol
FortiAuthenticator also supports Online Certificate Status Protocol (OCSP), defined in RFC 2560. To use OCSP, configure the FortiGate unit to use TCP port 2560 on the FortiAuthenticator IP address.
For example, configuring OCSP in FortiGate CLI for a FortiAuthenticator with an IP address of 172.20.120.16, looks like this:
config vpn certificate ocsp-server
edit fac_ocsp
set cert "REMOTE_Cert_1"
set url "http://172.20.120.16:2560"
end
Trusted CAs
Trusted CA certificates can be used to validate certificates signed by an external CA.
To view the trusted CA certificate list, go to Certificate Management > Certificate Authorities > Trusted CAs.
The certificate ID, subject, issuer, and status are shown. Certificates can be imported, exported, deleted, and searched.
To import a trusted CA certificate:
- From the trusted CA certificate list, select Import. The Import Signing Request or Trusted CA Certificate window opens.
- Enter a certificate ID in the Certificate ID field.
- In the Certificate field, Select Browse... to locate the file on your computer, then select OK to import the list.
When successful, the trusted CA certificate will be displayed in the list on the FortiAuthenticator device. You can select it to see the details (see To view certificate details:).
